I am going to discuss about TimeFinder BCV Split operation where Host running on Oracle Database. This split operation is different from normal BCV split operation. There are differences in command as well. Thats reason I am putting steps for this:
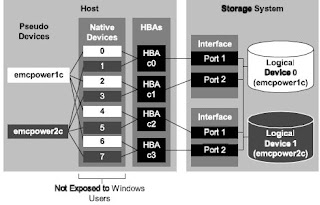
The following steps describes splitting BCV devices that hold a database supporting a host running an Oracle database. In this case, the BCV split operation is in an environment without PowerPath or ECA. The split operation described here suspends writes to a database momentarily while an instant split occurs. After an establish operation and the standard device and BCV mirrors are synchronized, the BCV device becomes a mirror copy of the standard device. You can split the paired devices to where each holds separate valid copies of the data, but will no longer remain synchronized to changes when they occur.
The Oracle database is all held on standard and BCV devices assigned to one Oracle device group.
1) Check device status on the database BCVs
To view and check status of the database BCV pairs, use the following form:
symmir –g DgName query
Check the output to ensure all BCV devices listed in the group are in the synchronized state
2) Check and set the user account
For SYMCLI to access a specified database, set the SYMCLI_RDB_CONNECT environment variable to the username and password of the system administrator’s account. The export action sets this variable to a username of system and a password of manager, allowing a local connection as follows:
export SYMCLI_RDF_CONNECT=system/manager
The ORACLE_HOME command specifies the location of the Oracle binaries and the ORACLE_SID command specifies the database instance name as follows:
export ORACLE_HOME=/disks/symapidvt/oraclhome/api179
export ORACLE_sid=api179
You can test basic database connectivity with the symrdb command as follows:
symrdb list –type oracle
3) Backup the database
For safety, perform a database hot backup. For example:
symioctl begin backup –type oracle –nop
4) Freeze the database
For safety, perform a freeze on the database I/O. For example:
symioctl freeze –type oracle –nop
This command suspends writes to the Oracle database.
5) Split all BCV devices in the group
To split all the BCV devices from the standard devices in the database device group, enter:
symmir –g oraclegrp split –instant -noprompt
Make sure the split operation completes on all BCVs in the database device group.
6) Thaw the database to resume I/O
To allow writes to the database to resume for normal operation, enter:
symioctl thaw –type oracle –nop
7) End the backup
To terminate the hot backup mode, enter the following command:
symioctl end backup –type oracle –nop